Gallery Photos

Guidelines For Phone Hacking Prevention
If yourphoneends up in the wrong hands, someone could steal your identity, buy stuff with your money, or hack into your email or social media accounts. Here's how to protect yourphone.
View Gallery & Article
Getting A Job In A Cytopathology Industry
American Society ofCytopathology(ASC) - Find your next career at CytoJobs. Check back frequently as newjobsare posted every day.
View Gallery & Article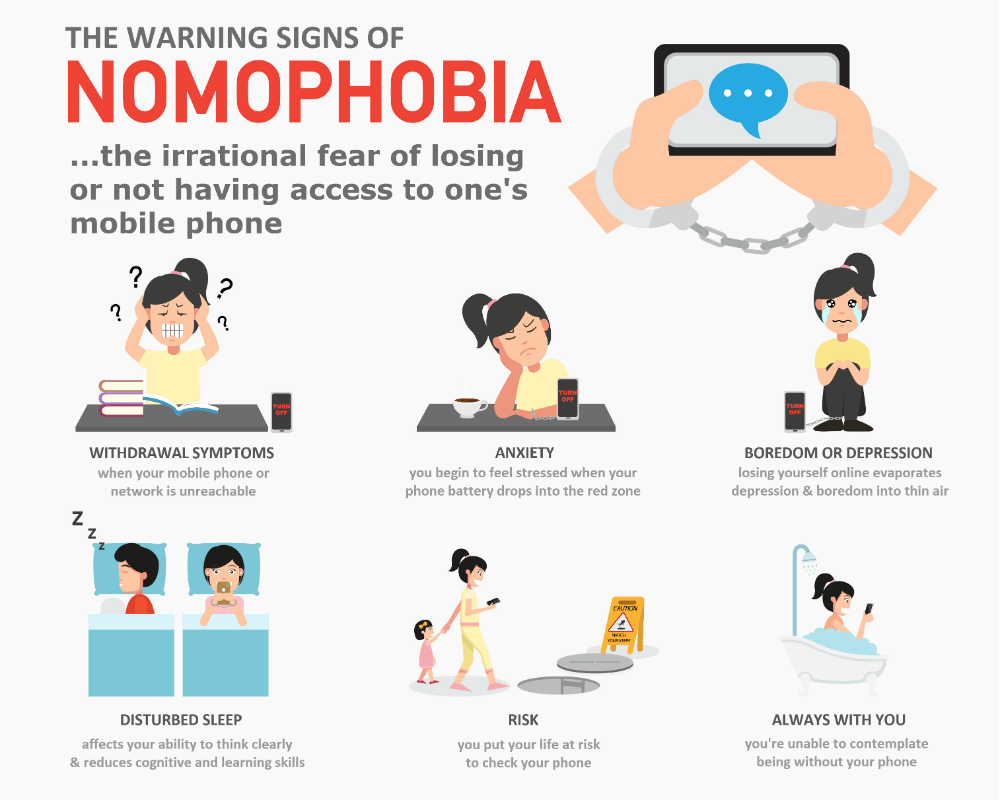
Nomophobia And Technology Addiction
Nomophobiais the fear of not accessing a mobile phone which has been recognised in the literature as a series of feelings and symptoms experienced by mobile/smartphone users. In the same manner, distraction andaddictionhave been found to interact with increasing usage and impact on users' wellbeing. This study aimed to explore the relationship betweennomophobiaanddistraction-addiction...
View Gallery & Article
Ways To Secure Your Digital Footprint Online
Apr 16, 2024Identity theft and fraud protection for your finances, personal info, and devices. Adigitalfootprint, otherwise known as an "electronicfootprint," is a record of youronlinepresence — a trail of sites you've visited, emails you've sent, and data you've left behind. Whether you ...
View Gallery & Article
Antiphishing Safeguard In Business Networks
Learn everything you need to know aboutanti-phishingsolutions and the top software on the market to give yourbusinessthe protection it needs.
View Gallery & Article
Pet Grooming At Home Prices
Comparepetgroomingpricesacross cities, services, andpettypes. Find the best rates for salon, mobile, and house callgroomingservices.
View Gallery & Article
Dell Laptop Hard Drive Replacement
Feb 4, 2026Learn how to replace aDelllaptopharddrive. Find step-by-step instructions for installation, operating system setup, and driver installation.
View Gallery & Article
Electric Motorcycles For Commute
ElectricMotorcyclesWere Made For The DailyCommuteAn eco-friendly ride to work.
View Gallery & Article
Online Identity Protection
Jan 16, 2026We analyzed dozens ofidentitytheftprotectionservices based on cost, coverage, free trials and value. To find the strongest defenses, we looked at credit monitoring, dark web surveillance ...
View Gallery & Article