Ways to Protect Data from Unauthorized Disclosure: A Comprehensive Guide
In today's digital age, data security has become a top priority for businesses and individuals alike. The threat of unauthorized disclosure of sensitive data is ever-present, and the consequences of a data breach can be severe. Therefore, it is essential to implement robust strategies to protect data from unauthorized disclosure.
Understanding the Risks of Data Disclosure
Data disclosure occurs when sensitive information is released or accessed without proper authorization. This can happen due to various reasons such as hacking, phishing, or human error. Unauthorized disclosure can lead to reputational damage, financial losses, and even lawsuits for non-compliance with regulations such as GDPR and HIPAA.

Ways to Protect Data from Unauthorized Disclosure
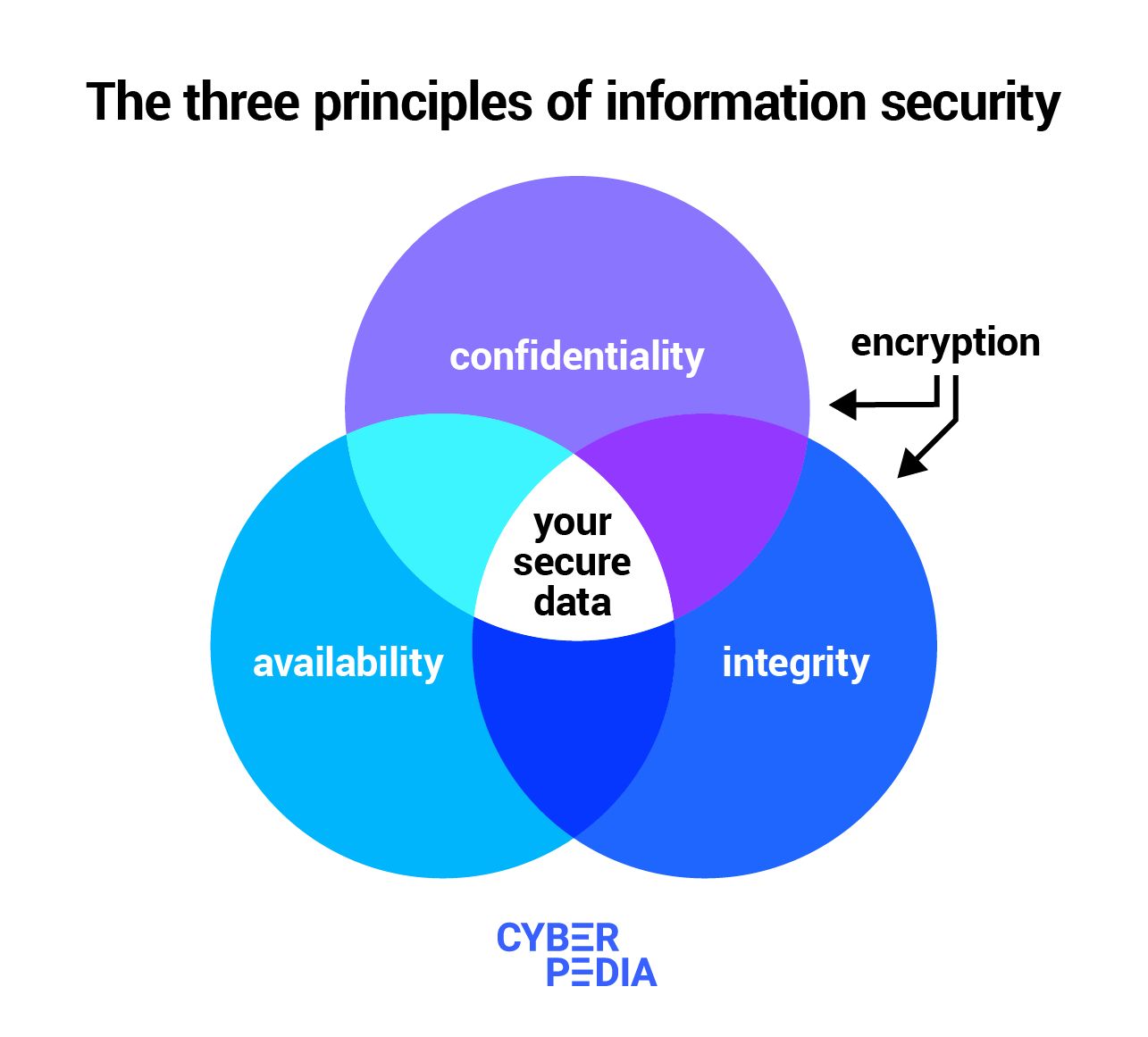
- Data Classification:**Classify sensitive data into different categories based on their level of confidentiality, integrity, and availability. This helps in implementing appropriate security measures to protect the data.
- Data Encryption:**Use encryption to protect data both in transit and at rest. Encryption makes it difficult for unauthorized individuals to access and read the data.
- Data Access Control:**Implement role-based access control (RBAC) to restrict access to sensitive data based on user roles and permissions.
- Data Backup and Recovery:**Regularly back up sensitive data and implement disaster recovery procedures in case of data loss or corruption.
- Data Monitoring and Logging:**Implement data monitoring and logging to track all access and modifications to sensitive data.
- Data Training and Awareness:**Regularly educate employees on data security best practices to prevent data breaches and unauthorized data disclosure.
- Data Review and Audit:**Regularly review and audit sensitive data to identify potential security threats and vulnerabilities.
Data classification involves identifying, categorizing, and categorically labeling the sensitivity of data, which can be public, private, or confidential. This process helps in implementing robust security measures to protect the data. For instance, sensitive data such as financial information and personal identifiable information (PII) should be handled with greater care than less sensitive data such as public records.
Data encryption is a process of converting plaintext data into unreadable ciphertext to protect against unauthorized access. Encryption can be implemented using various algorithms such as AES and SSL/TLS. Data encryption can be used to protect data both in transit and at rest. This means that even if data is intercepted or accessed without authorization, it will remain unreadable until the decryption key is applied.
Role-based access control (RBAC) is a mechanism of restricting access to systems, applications, and data based on user roles and permissions. RBAC involves assigning specific roles to users, which defines their level of access to sensitive data. For instance, a user with an administrator role may have access to all data, while a user with a reader role may only have access to public data.
Data backup and recovery is an essential process that involves creating copies of sensitive data and storing them in a secure location. This ensures that data is not lost in case of system failure, theft, or natural disasters. Data backup and recovery procedures should be regularly tested to ensure their effectiveness.
Data monitoring and logging involve tracking all access and modifications to sensitive data. This helps in identifying potential security threats and detecting unauthorized data disclosure. Data monitoring and logging may involve tracking user activities, network traffic, and system logs.
Data security training and awareness is an essential process that involves educating employees on data security best practices. This includes teaching employees about data handling policies, password management, and phishing attacks. Regular data security training and awareness can help prevent data breaches and unauthorized data disclosure.
Data review and audit is a process that involves reviewing and analyzing sensitive data to identify potential security threats and vulnerabilities. This helps in identifying data breaches, non-compliance with regulations, and potential security risks. Data review and audit may involve regularly scanning for malware, tracking user activities, and monitoring system logs.