Ways to Protect Data from Unauthorized Access
Looking to prevent unauthorized access to your data? This article will guide you through effective strategies to safeguard your systems and sensitive information.
Understanding Unauthorized Access
Unauthorized access refers to individuals gaining access to an organization's data, networks, endpoints, applications, or devices without permission. It is closely related to authentication, a process that verifies a user's identity when they access a system.
Why Protecting Data is Crucial
Data security and privacy are key concepts that protect sensitive information from unauthorized access, breaches, and misuse. Data security protects data from external and internal dangers using various protective measures.
Common Attack Methods
- Weak or stolen passwords: Weak passwords, password reuse, and single-factor authentication remain leading causes of unauthorized access. Attackers can easily guess or crack simple credentials, and stolen login data is widely available through phishing or data breaches.
- Phishing and social engineering: Attackers use psychological manipulation to trick users into divulging sensitive information or performing certain actions that compromise security.
- Ransomware and malware: Malicious software can encrypt or delete data, demanding payment in exchange for restoration or threat of exposure.
Best Practices for Data Protection
Implementing Robust Password Security
Use strong, unique passwords for each account, and consider using a password manager to securely store and generate complex passwords. Enable multi-factor authentication to add an extra layer of security.
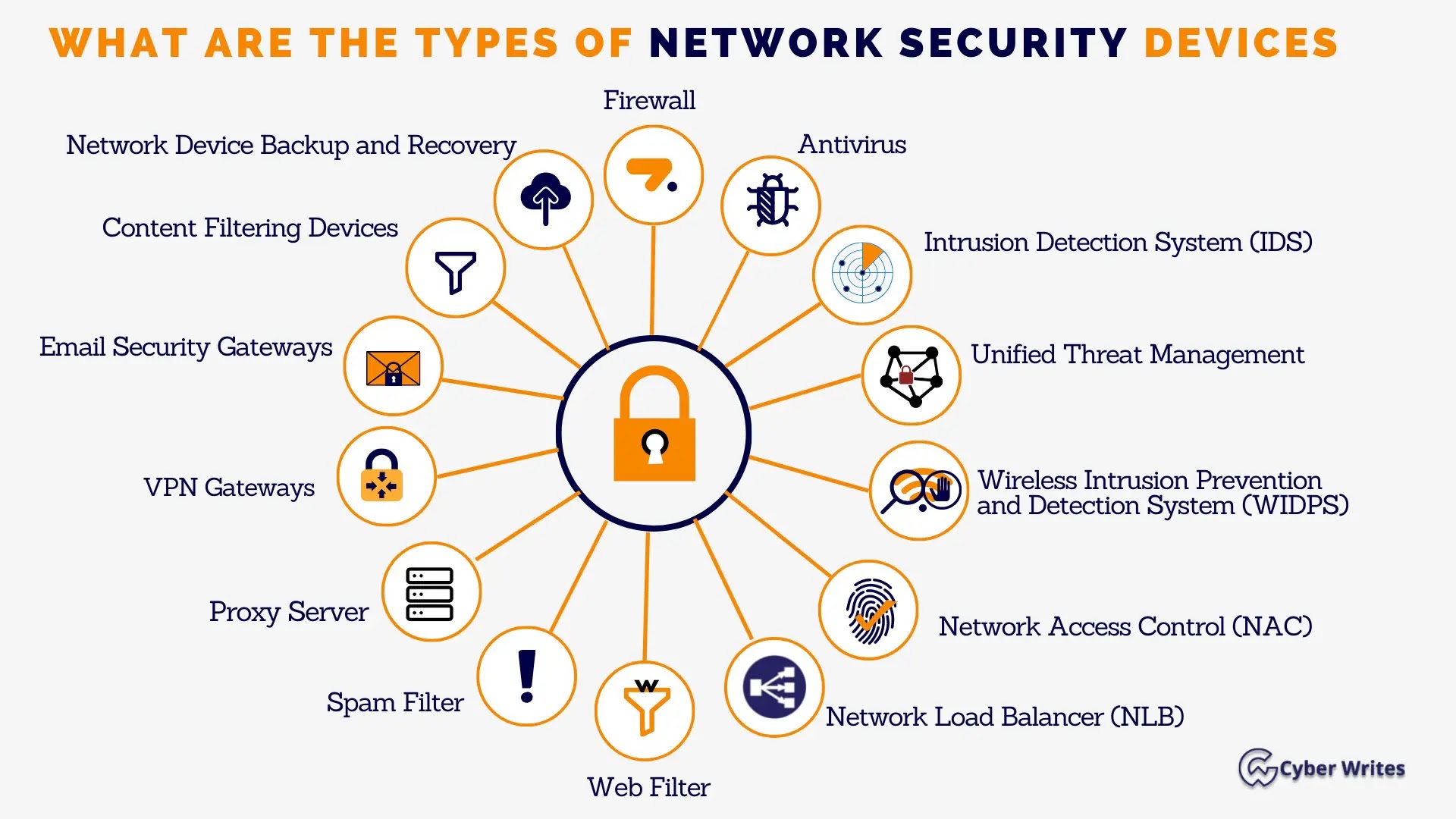
Firewall Configuration
Configure firewalls to control network traffic and prevent unauthorized access. Firewalls are designed to protect networks from unauthorized access and malicious traffic.
Data Encryption
Encrypt sensitive data both in transit and at rest using secure protocols like HTTPS and AES. This ensures that even if data is intercepted or accessed without permission, it will be unreadable and unusable.

Regular Software Updates
Keep software up to date to patch security vulnerabilities and prevent exploitation by attackers.
Secure E-mail Handling
Use secure e-mail protocols like S/MIME and PGP to encrypt email communications and prevent interception or eavesdropping.
Tools and Software for Data Protection
Consider using tools and software that provide an additional layer of security, such as:
- My Lockbox: An advanced software tool that enables users to lock folders on their computer, providing a secure way to protect and password-protect sensitive data from unauthorized access.
- Private Box: A software tool that allows users to create a secure virtual box to store and protect sensitive files, photos, and videos.
- Firewalls and antivirus software: Essential tools for protecting networks and systems from unauthorized access and malware.
Best Practices for Database Security
Implement robust security measures for databases, including:
- Password protection: Use strong, unique passwords and multi-factor authentication to secure database access.
- Access controls: Implement role-based access control to restrict database access to authorized personnel.
- Data encryption: Encrypt sensitive data stored in the database using secure protocols.
- Regular backups: Regularly back up databases to prevent data loss in case of a breach or system failure.
Conclusion
Protecting data from unauthorized access is crucial for maintaining confidentiality, integrity, and availability of sensitive information. By understanding common attack methods and implementing robust security measures, organizations can safeguard their systems and sensitive information from unauthorized access and misuse.
Stay vigilant and take proactive steps to protect your data from unauthorized access. Remember, data security is everyone's responsibility, and together we can create a safer digital environment.