Phishing Threats for Personal Laptop: A Comprehensive Guide
Phishing threats for personal laptop have become a significant concern in today's digital world. With the rise of cyber attacks, it's essential to be aware of the tactics used by scammers to steal sensitive information. In this article, we'll delve into the world of phishing and provide you with valuable insights on how to protect your laptop from these threats.
What are Phishing Threats?
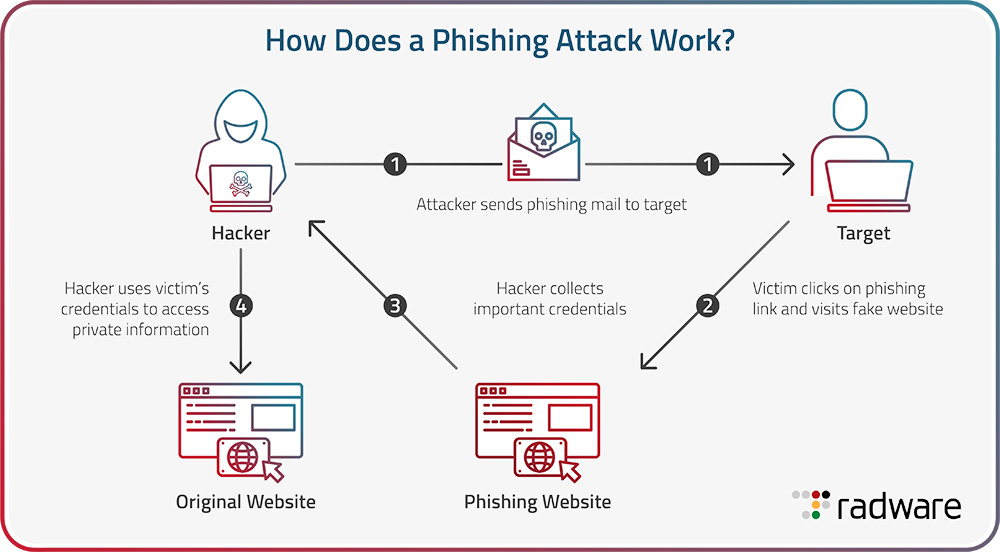
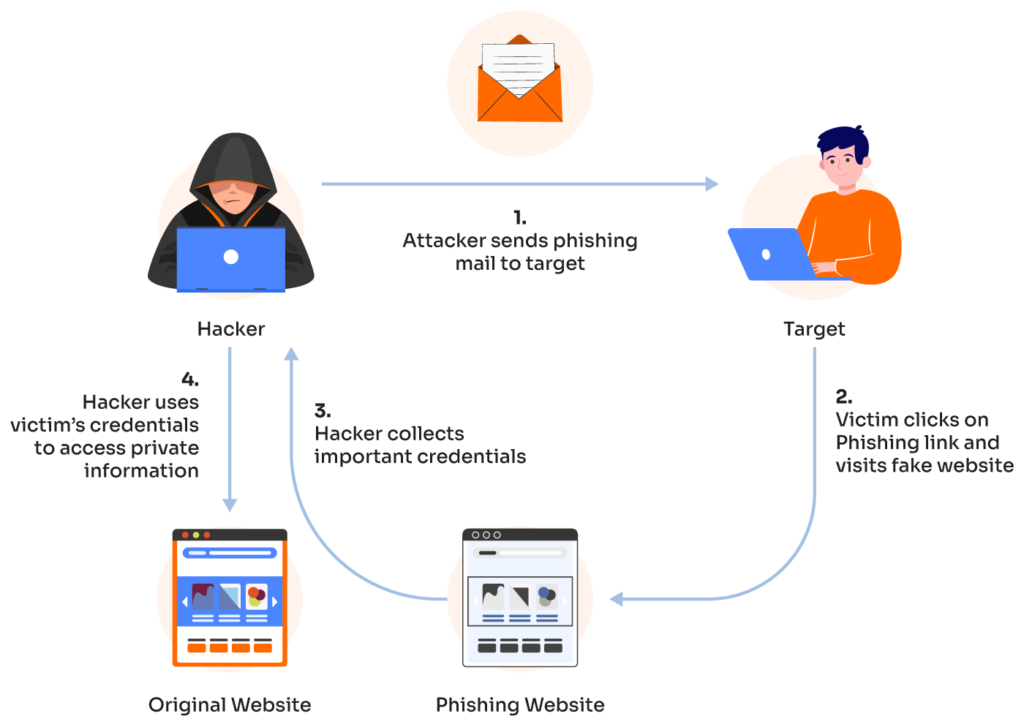
Phishing attacks involve tricking individuals into revealing sensitive information by masquerading as a reputable entity or person. Scammers use various means, including emails, texts, or phone calls, to extract personal information such as passwords, credit card details, or Social Security numbers. This information can be used to gain unauthorized access to your accounts or even sell it to other scammers.
Types of Phishing Attacks
Phishing by Email
Phishing by Text Message (Smishing)
Phishing by Phone Call (Vishing)
Spear Phishing: Targeted attacks on specific individuals or groups
Whaling: Phishing attacks targeting high-level executives or individuals
Pharming: Redirecting users to fake websites to steal sensitive information
Identifying Phishing Threats
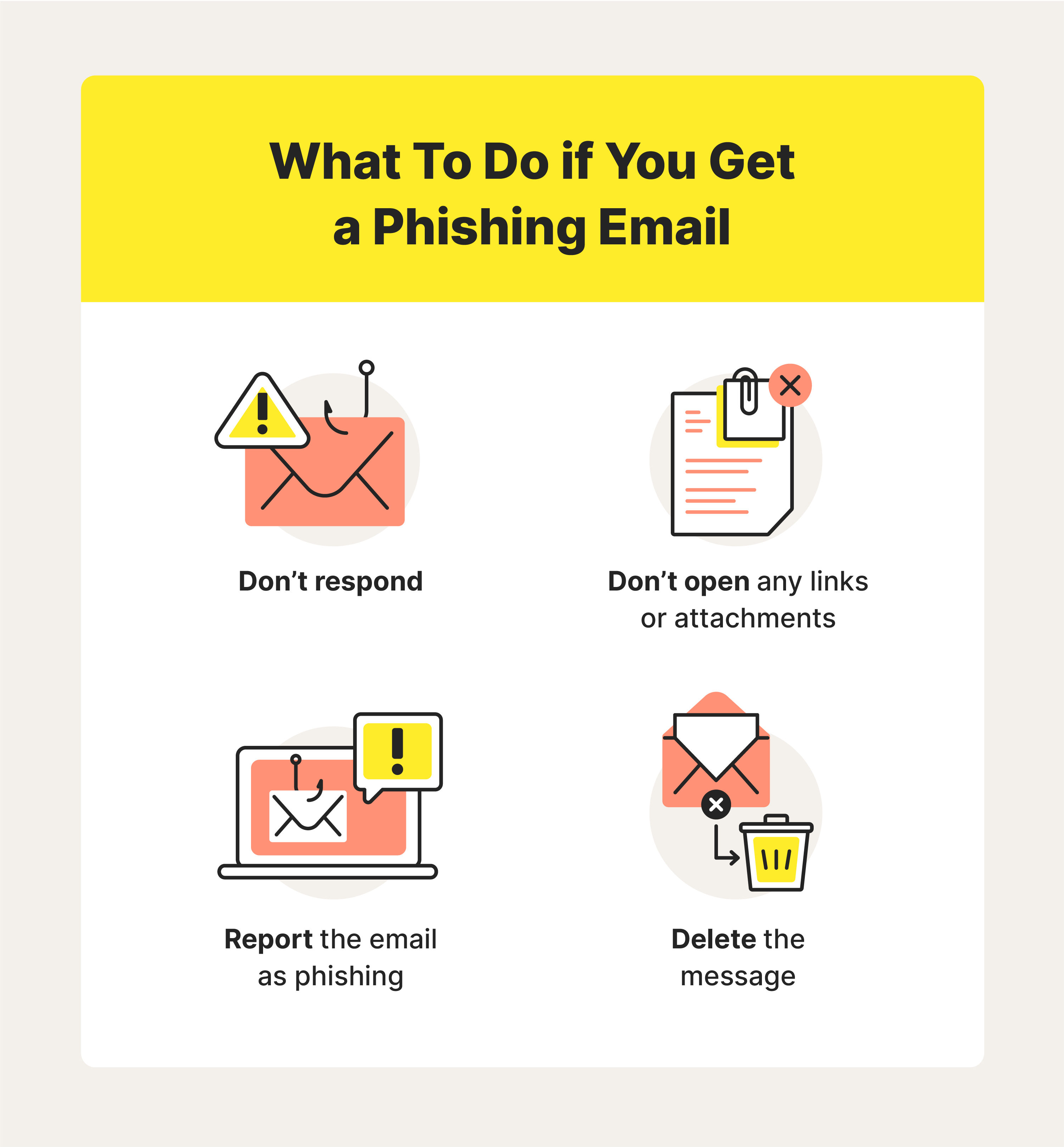
To stay safe, it's essential to recognize the signs of a phishing attack. Look out for:

Spelling and grammar mistakes in the email or message
Urgent or threatening language to create a sense of panic
Requests for sensitive information or financial details
Links or attachments from unknown sources
Protecting Your Laptop from Phishing Threats
To safeguard your laptop from phishing threats, follow these best practices:
Use antivirus software with real-time protection
Keep your operating system and browser up-to-date
Use strong, unique passwords and enable two-factor authentication
Be cautious when clicking on links or downloading attachments from unknown sources
Use a reputable VPN to encrypt your internet connection
Conclusion
Phishing threats for personal laptop are a persistent concern in today's digital landscape. By understanding the tactics used by scammers and taking proactive measures to protect your laptop, you can minimize the risk of falling victim to these attacks. Remember to stay vigilant, be cautious of suspicious emails and messages, and always prioritize your cybersecurity.