Malware Fugues: Understanding the Complex Forms of Digital Harassment
Malware, short for "malicious software," refers to a type of computer program designed to infect a legitimate user's computer and inflict harm on it in multiple ways. In this article, we will delve into the concept of malware fugues, a modern, complex form of digital harassment that can be just as elusive and formidable as its musical counterpart.
What are Malware Fugues?
A malware fugue refers to a sophisticated, adaptive form of malware that uses various techniques to evade detection and spread across digital domains. These malicious programs can infect computers, mobile devices, and networks, causing significant damage to software systems, stealing sensitive data, and disrupting critical operations. Malware fugues are often designed to persist indefinitely, making them a persistent threat to digital security.
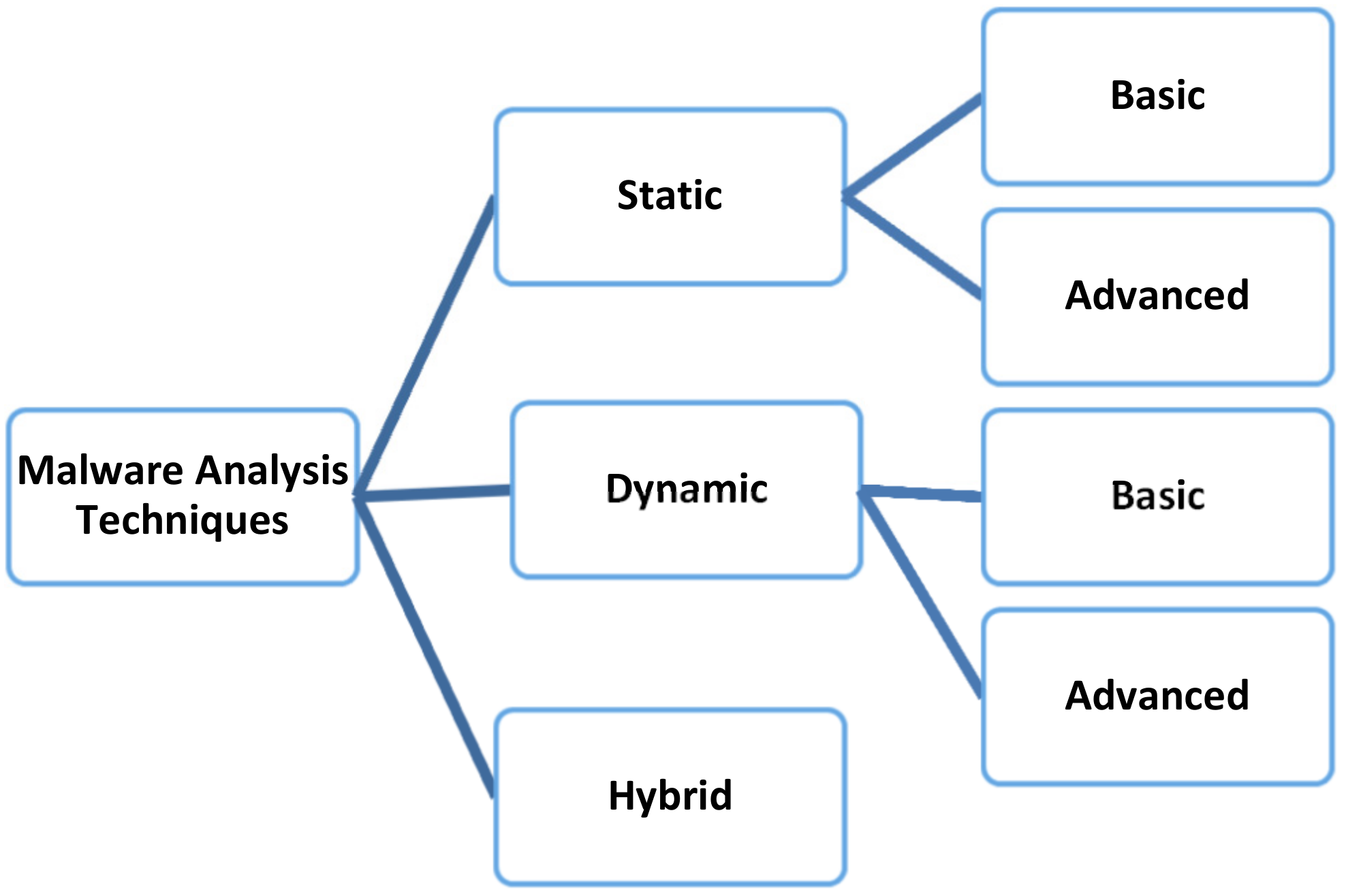
Types of Malware and Their Evolution
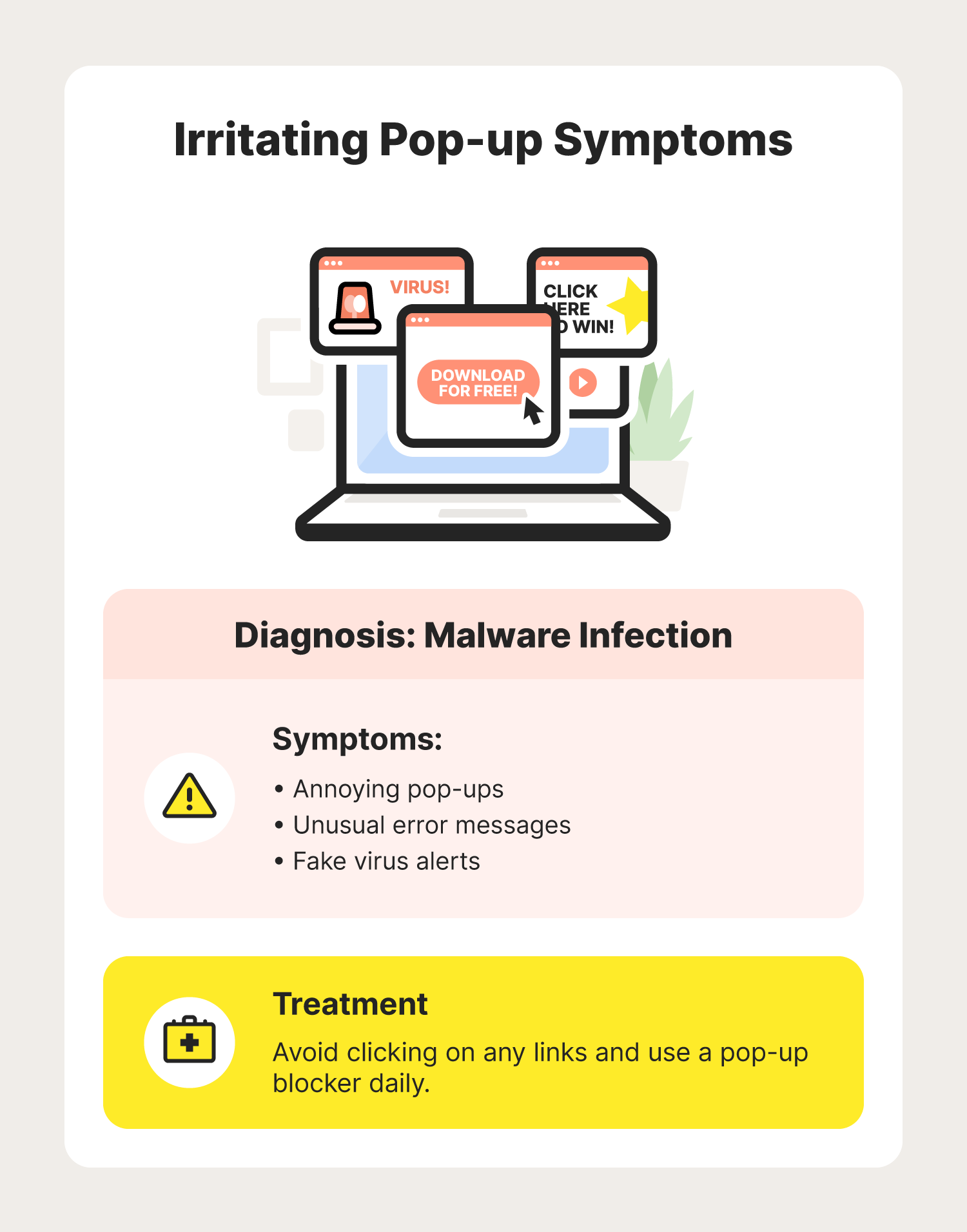
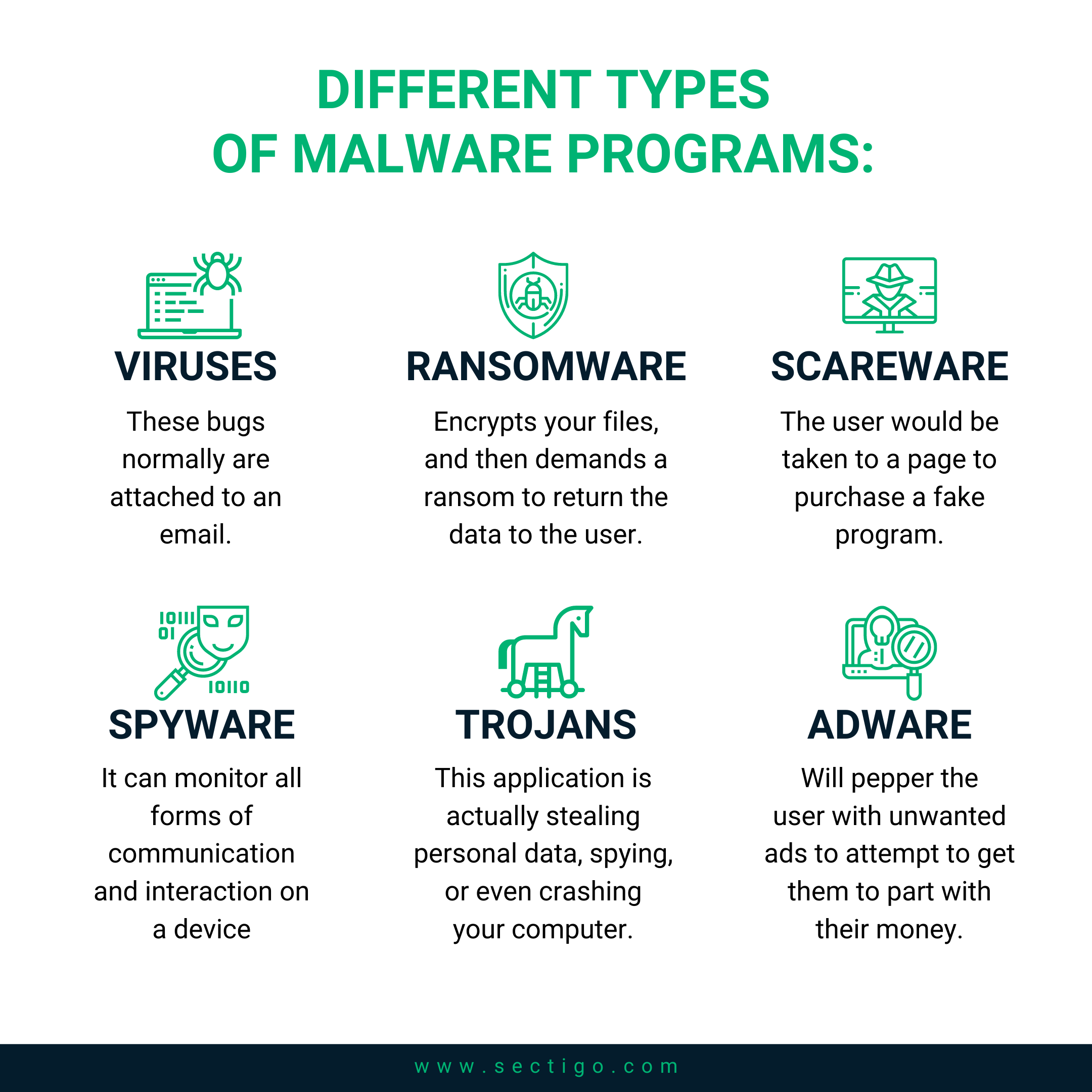
Malware comes in various forms, including adware, spyware, viruses, worms, Trojans, ransomware, rootkits, keyloggers, cryptominers, and exploits. Each type of malware has evolved over time, becoming increasingly complex and sophisticated. For instance, ransomware has evolved from simple encryption techniques to sophisticated, multi-stage attacks, while adware has transformed from simple pop-up ads to sophisticated tracking and profiling mechanisms.
These modern forms of malware have given rise to the concept of malware fugues, which aim to evade detection by using advanced techniques such as code obfuscation, encryption, and sandbox evasion.
Characteristics of Malware Fugues
Malware fugues exhibit several characteristics that distinguish them from traditional malware:
- Persistent presence: Malware fugues can persist on a system even after a reboot or a basic sweep of malware removal tools.
- Adaptive behavior: These malicious programs adapt and evolve over time, making them increasingly difficult to detect and remove.
- Fierarchical structure: Malware fugues often have a hierarchical structure, with multiple layers of encryption and communication protocol.
- Networked operations: These programs can communicate with command and control centers, sharing data and receiving instructions in real-time.
- Memory-residency: Malware fugues can remain resident in memory, even after the infected system is shut down or power-cycled.
Consequences of Malware Fugues
The consequences of malware fugues can be devastating, including:

Crafting Effective Countermeasures
To combat the menace of malware fugues, system administrators and security professionals must adopt a multi-layered approach:

![How to Remove Adware, Trojans, Virus & Malware from Windows [Guide] How to Remove Adware, Trojans, Virus & Malware from Windows [Guide]](https://dfzljdn9uc3pi.cloudfront.net/2022/cs-1092/1/fig-2-full.png)