Ransomware Protection For Virtual Machines: A Comprehensive Guide
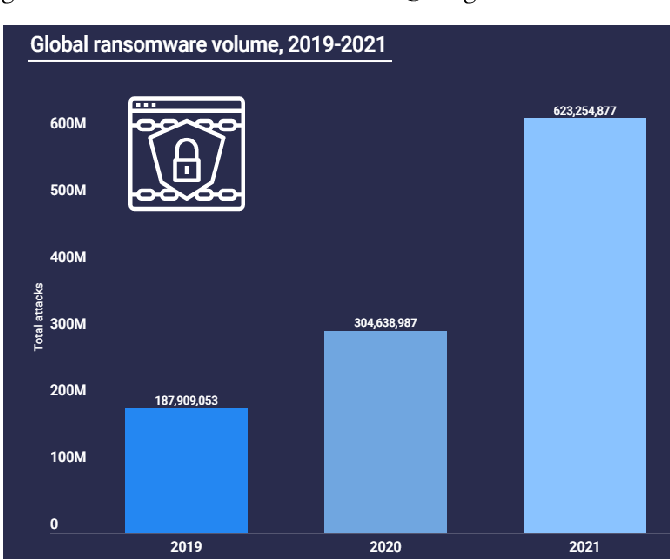
In today's digital landscape, virtual machines (VMs) have become an essential component of many organizations' IT infrastructure. However, with the growing threat of ransomware attacks, protecting these virtual machines has become a top priority. In this article, we will delve into the world of ransomware protection for virtual machines, exploring the latest threats, best practices, and solutions to safeguard your VMs against these malicious attacks.What is Ransomware Protection For Virtual Machines?
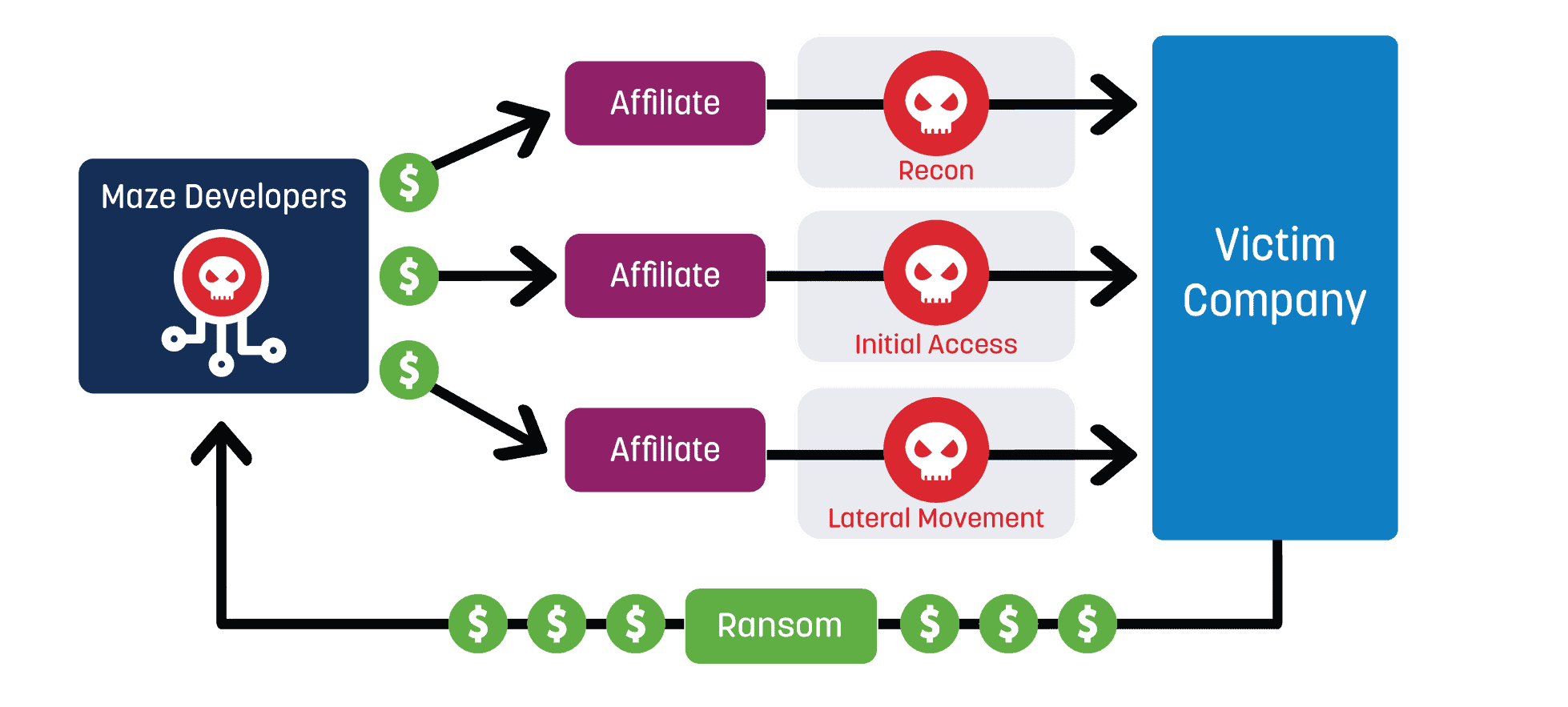
Ransomware protection for virtual machines refers to the measures taken to prevent, detect, and respond to ransomware attacks targeting VMs. This includes implementing security controls, monitoring and analysis, and backup and recovery strategies to minimize the impact of a ransomware attack.Why Are Virtual Machines A Target for Ransomware Attackers?
VMs are particularly attractive to ransomware attackers due to their ability to store and process large amounts of sensitive data. Additionally, VMs often have a high value to the organization, making it more lucrative for attackers to target them. Furthermore, VMs can be easily orchestrated and managed, making it simpler for attackers to spread their malware and encrypt the VMs.Best Practices for Ransomware Protection For Virtual Machines
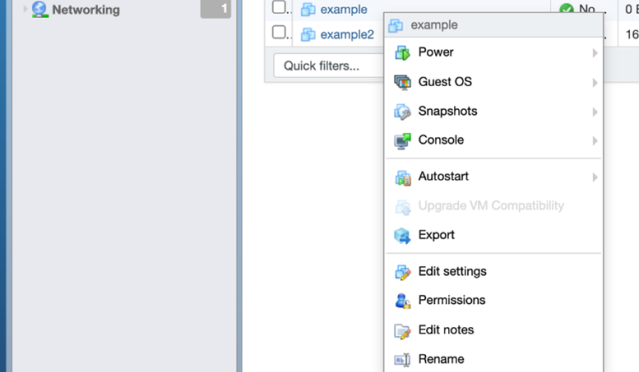
To protect your virtual machines from ransomware attacks, follow these best practices:- Implement Regular Backups: Ensure that you have a robust backup and recovery process in place, including regular snapshots and incremental backups. This will allow you to quickly recover your VMs in the event of a ransomware attack.
- Use Secure VM Images: Use secure and up-to-date VM images that have been patched and updated to minimize the attack surface.
- Enable Anti-Ransomware Capabilities: Enable anti-ransomware capabilities in your backup software to detect and eliminate ransomware malware during the backup process.
- Use Monitoring and Analysis Tools: Implement monitoring and analysis tools to detect and respond to potential ransomware attacks in real-time.
- Implement Access Controls: Implement strict access controls to limit user access to VMs and sensitive data.
- Use Encryption: Use encryption to protect data stored on VMs and in transit.
- Regularly Update and Patch: Regularly update and patch your VMs and software to minimize the attack surface.
- Train Users: Train users to recognize and report potential ransomware attacks.

Solutions for Ransomware Protection For Virtual Machines
To protect your virtual machines from ransomware attacks, consider the following solutions:- Backup and Recovery Software: Use backup and recovery software that provides anti-ransomware capabilities, such as Veeam or Veritas.
- Security Information and Event Management (SIEM) Systems: Implement SIEM systems to detect and respond to potential ransomware attacks in real-time.
- Endpoint Detection and Response (EDR) Tools: Use EDR tools, such as Crowdstrike or Carbon Black, to detect and respond to potential ransomware attacks.
- Cloud-Based Security Solutions: Consider cloud-based security solutions, such as Microsoft Defender for Cloud or AWS Security Hub, to provide advanced threat protection and detection.