Data erasure, also known as secure deletion, data clearing, or data wiping, is a software-based method of data sanitization that aims to completely destroy all electronic data residing on a hard disk drive or other digital media by overwriting data onto all sectors of the device in an irreversible process. This operation is essential for achieving confident data destruction and avoiding unauthorized access to sensitive information.
In today's digital age, the importance of data erasure cannot be overstated. Whether you are an individual seeking to dispose of outdated hardware or an organization with data disposal needs, understanding various secure data erasure methods is crucial. This article will guide you through the significance of data erasure, its relevance to data destruction, and explore the various methods available for effective data sanitization.
Data erasure methods vary in complexity, risk, and usability. Your choice of method should depend on the type of data, storage media, and your organization's data security requirements. Some widely used methods include:
- Overwriting Method: This involves writing random patterns over previously existing data on a storage device. Overwriting methods come in different forms, such as a 1-pass, 3-pass, or 7-pass process. Each has its level of thoroughness in erasing data. The number of passes determines the level of data erasure.
- Cryptographic Erasure: This method uses cryptography to ensure that data can only be accessed by authorized parties with the decryption key. Extensive use of encryption makes data recovery extremely difficult, effectively rendering it unusable.
- Physical Destruction: This is a physical process where media, such as hard drives or any other electronic storage devices, are destroyed to a degree that they cannot be recovered.
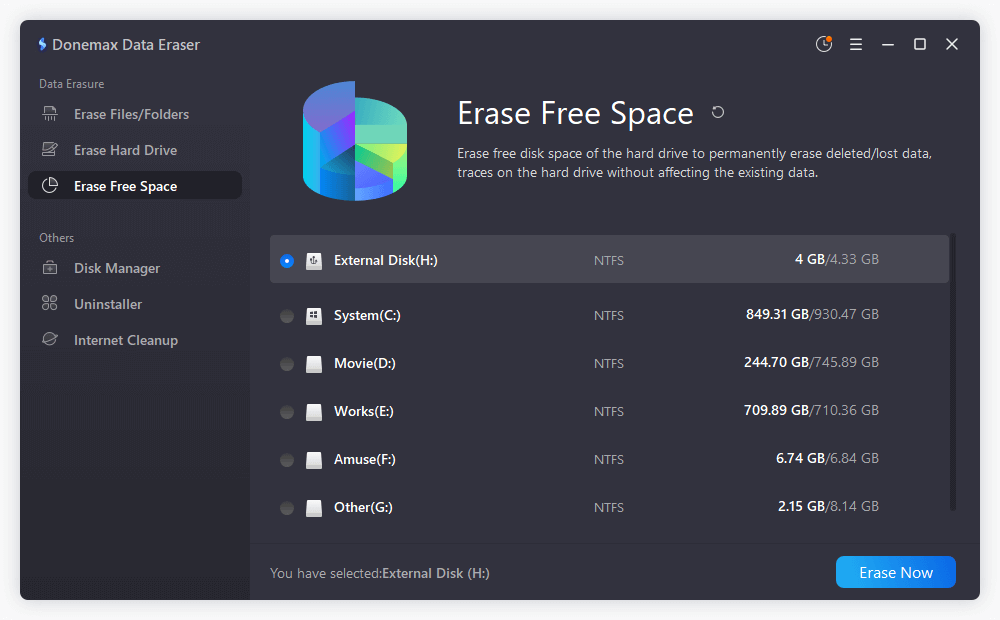
- Software-Based Erasure: Utilizes software to wipe or erase data from a storage device. These programs are vital for sanitized data erasure processes, especially on SSDs, which can be challenging to erase using traditional methods.
Secure erasure is a critical process due to the high risks of data breaches. Unauthorized access to sensitive information can have far-reaching and devastating consequences. Using certified data erasure procedures ensures that any data left on devices cannot be retrieved or used maliciously. A well-organized erasure process also contributes to the protection of both your company's reputation and to adhere to regulations requiring data destruction and erasure.
Several factors must be considered when selecting a method for secure data erasure, including the type of storage devices, the nature of the data being erased, and the level of data security desired. An understanding of the different options available is crucial. Professional data erasure software can offer various methods tailored to specific needs, offering a variety of techniques, from basic overwrite methods to more complex cryptographic erase techniques. Devices such as hard drives, solid-state drives, and memory devices can each require different methods for complete data sanitization.
Modern solid-state drives, through firmware-level translation and wear level-based operations, present a unique challenge to secure erasure. NIST SP 800-88 Rev. 1-compliant methodologies are designed to achieve verifiable data sanitization, even on these newer devices. Utilizing certified methodologies like NIST SP 800-88 Rev. 1 ensures that sensitive data is irretrievable.
Continual updates in technology mean that software erasure kits must stay up-to-date to handle new challenges posed by updated hardware. Requirements may vary depending on each device's technical specifications and the type of erasure sought. Always employ industry-recognized guidelines, such as those provided by NIST 800-88, for erasure methods on multimedia. In a world where cyber data breaches are on the rise, it is inherently necessary to prioritize confidentiality within both storage and erasure processes.