Protecting Data Against Ransomware: A Comprehensive Guide to Prevention and Mitigation
Ransomware, a type of malicious software that encrypts and locks files, has become a significant threat to organizations worldwide. In recent years, ransomware attacks have surged, resulting in substantial financial losses and compromised data. As such, it's essential for organizations to develop a robust strategy to protect against ransomware and ensure business continuity.
Understanding Ransomware
Ransomware is software that encrypts files and demands a ransom in exchange for the decryption key. It can spread through various means, including phishing emails, compromised software, and vulnerable networks. Once a system is infected, the attacker can demand payment in exchange for unlocking the encrypted data or threatening to delete the data indefinitely.
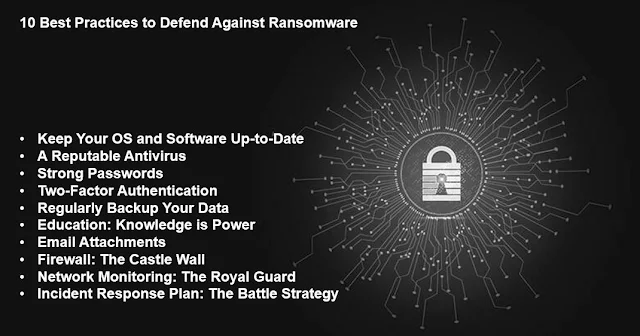
Protecting Against Ransomware
Protecting against ransomware requires a comprehensive approach that includes prevention, detection, and response strategies. Here are some best practices to help organizations safeguard their data against ransomware:
- Implement Regular Backups:** Regular backups are essential for recovery in the event of a ransomware attack. Ensure that backups are stored on separate devices and maintained offline to prevent data loss.
- Keep Software Up-to-Date: Regularly update operating systems, applications, and software to prevent exploitation of known vulnerabilities.
- Implement Strong Authentication:** Use strong authentication methods, such as multi-factor authentication, to prevent unauthorized access to systems and data.
- Use Security Software:** Install reputable security software that includes antivirus, anti-malware, and firewall components to detect and prevent ransomware infections.
- Train Employees:** Educate employees on cybersecurity best practices, including safe browsing habits, email phishing recognition, and password management.
responding to Ransomware Attacks
In the unfortunate event of a ransomware attack, it's critical to respond promptly and effectively. Here are some steps to take:
- Isolate the Infected System:** Isolate the affected system to prevent further spread of the ransomware.
- Containment and Eradication:** Contain the ransomware and eradicate it from the system to prevent re-infection.
- Recovery and Restoration:** Restore data from backups to prevent data loss and ensure business continuity.
- Incident Analysis:** Conduct a thorough analysis to identify vulnerabilities and areas for improvement to prevent future attacks.

Mitigation Strategies
Implementing mitigation strategies can significantly reduce the risk of a ransomware attack. Here are some mitigation strategies to consider:
- Implement a Cloud-Based Security Solution:** Utilize cloud-based security solutions that provide real-time threat detection, incident response, and vulnerability management.
- Use artificial Intelligence (AI) and Machine Learning (ML): Leverage AI and ML-powered security solutions to detect and prevent ransomware attacks.
- Implement Web Application Firewall (WAF): Utilize a WAF to protect web applications from known and unknown threats.
- Segment Networks and Systems:** Segment networks and systems to prevent lateral movement and contain the attack.
Conclusion
Protecting against ransomware requires a comprehensive approach that includes prevention, detection, and response strategies. By implementing regular backups, keeping software up-to-date, using strong authentication, using security software, and training employees, organizations can significantly reduce the risk of a ransomware attack. In the event of an attack, responding promptly and effectively can minimize data loss and ensure business continuity. By mitigating vulnerabilities and implementing additional security measures, organizations can further reduce the risk of a ransomware attack and safeguard their data.
Recommendations
Based on the best practices and mitigation strategies outlined above, here are some recommendations for organizations looking to protect against ransomware:
- Develop a Comprehensive Ransomware Response Plan:** Create a detailed plan that outlines procedures for prevention, detection, response, and mitigation.
- Conduct Regular Security Assessments:** Conduct regular security assessments to identify vulnerabilities and areas for improvement.
- Implement a Cloud-Based Security Solution:** Utilize a cloud-based security solution that provides real-time threat detection, incident response, and vulnerability management.
- Train Employees:** Educate employees on cybersecurity best practices, including safe browsing habits, email phishing recognition, and password management.