Malware Protection for Cloud Computing Infrastructure: A Comprehensive Approach
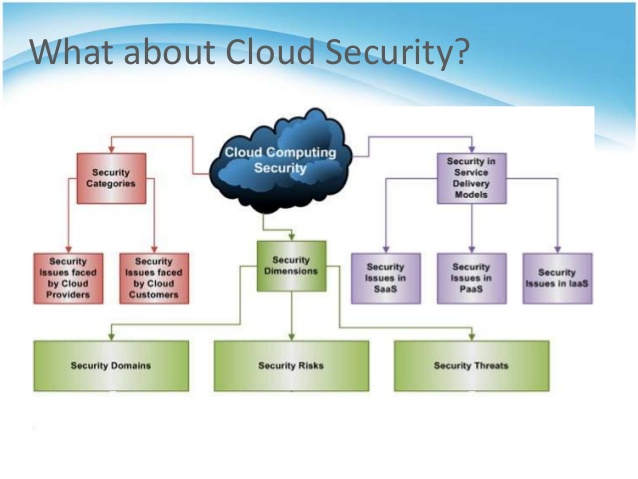
As the adoption of cloud computing continues to grow, the risks associated with malware attacks on cloud computing infrastructure are becoming increasingly significant. Despite its numerous benefits, cloud computing infrastructure is highly vulnerable to various security challenges, including malware. Therefore, extensive research towards detecting and safeguarding the cloud architecture against malware attacks is crucial.
Understanding the Risks Associated with Malware in Cloud Computing
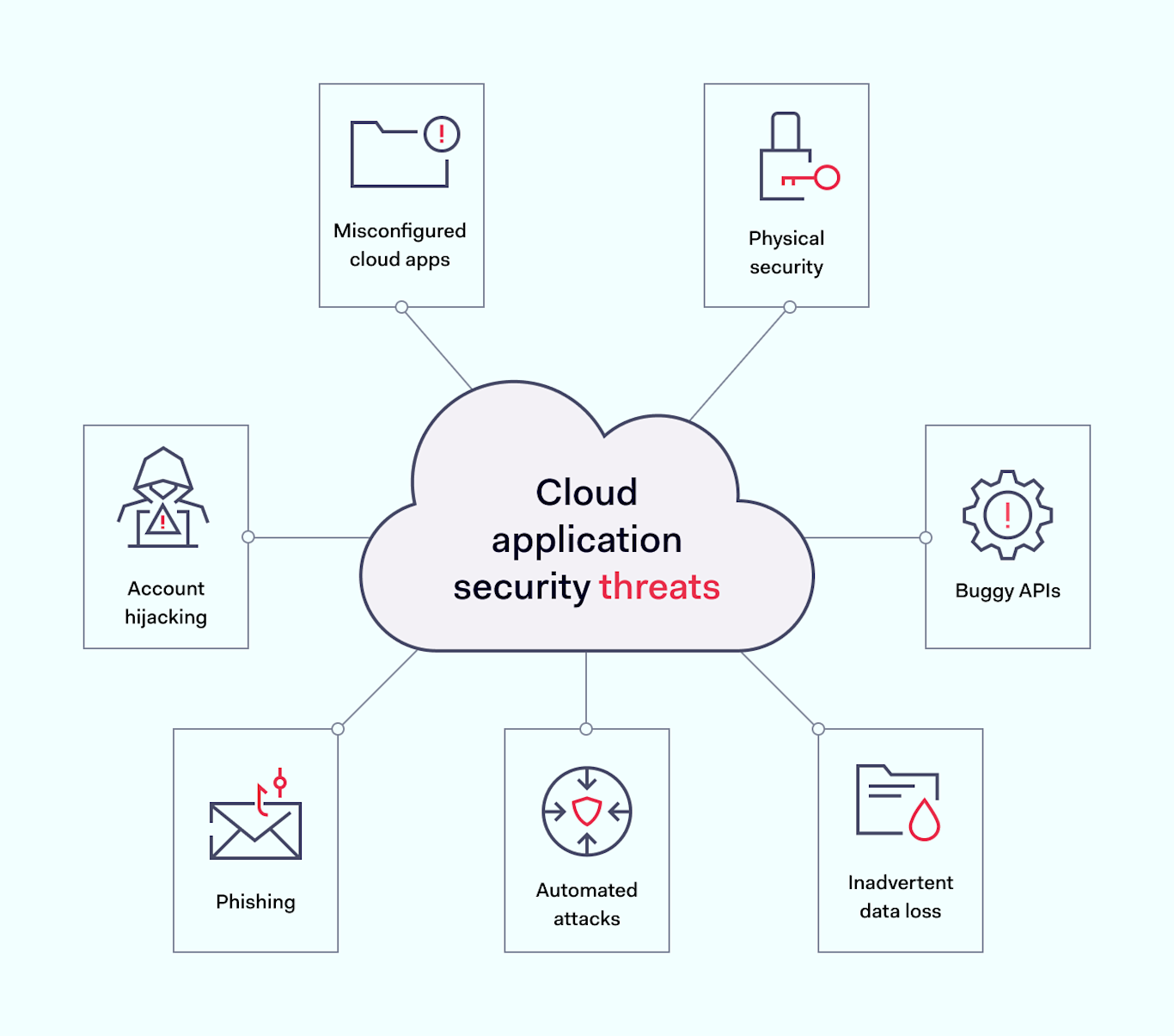
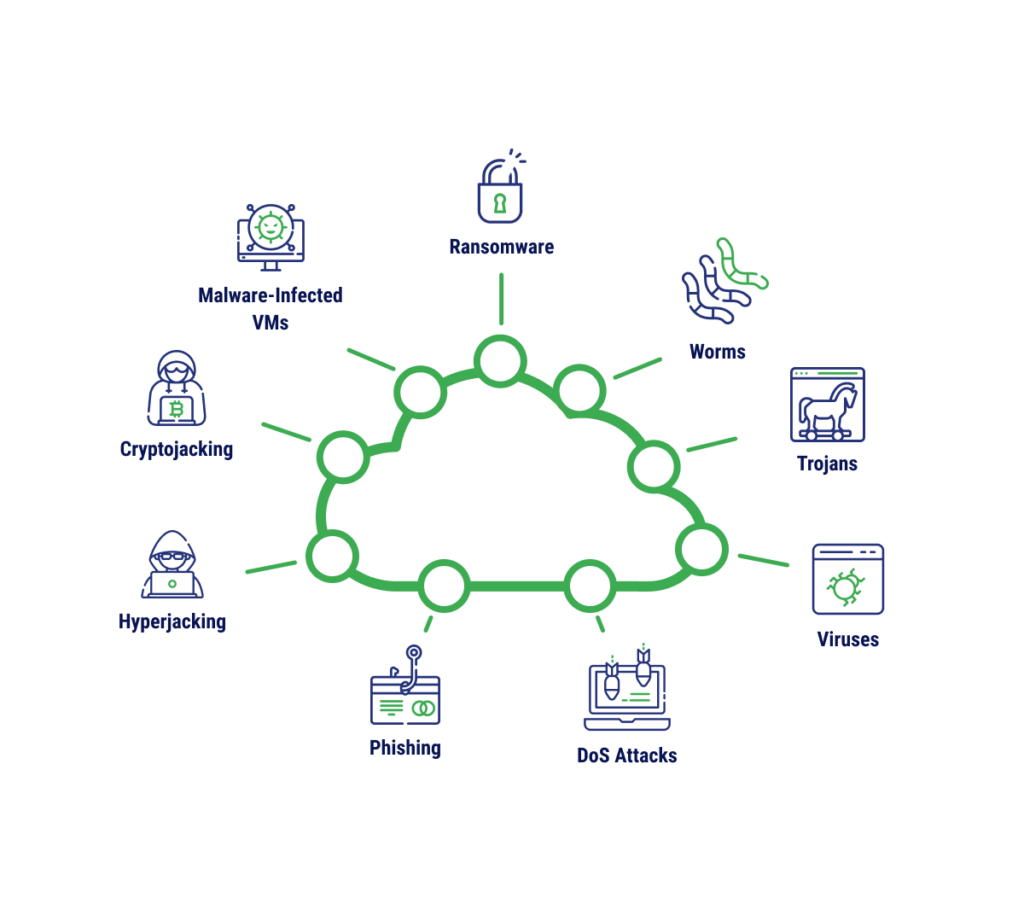
Malware, short for malicious software, is designed to harm or exploit a system without the owner's consent. In the context of cloud computing, malware can be particularly destructive, as it can spread quickly across the cloud infrastructure, compromising sensitive data and applications. The ease of deployment and scalability of cloud services make it an attractive target for cyber attackers.
Encryption is essential for securing data stored in the cloud.
Multi-factor authentication, endpoint protection, and regular security audits should be part of any cloud strategy.
Detecting and Preventing Malware in Cloud Computing
Detecting and preventing malware in cloud computing requires a multi-layered approach that combines traditional security controls with cloud-specific measures. This includes implementing cloud security posture management (CSPM) and cloud workload protection platform (CWPP) capabilities, such as Microsoft Defender for Cloud. Such platforms help protect environments across Azure, Amazon Web Services (AWS), Google Cloud Platform (GCP), and on-premises systems.
Cloud Malware: Rapid Detection and Resolution
The speed of detection and response is critical in preventing the spread of malware in cloud computing. By leveraging cloud-native applications, artificial intelligence, and machine learning, organizations can quickly identify and contain malware attacks. This includes implementing cloud-based sandboxing, which allows for the analysis of malicious files and traffic in a safe and controlled environment.

Conclusion
In conclusion, protecting against malware in cloud computing infrastructures is a critical aspect of cloud security. By adopting a proactive approach that includes implementing robust security controls, leveraging cloud-native applications, and investing in artificial intelligence and machine learning, organizations can effectively detect, prevent, and recover from malware attacks. This is essential for safeguarding sensitive data and applications in the cloud.
Cloud Security Best Practices
Some of the best practices of cloud security include:
Encryption
Multi-factor authentication
Endpoint protection
Regular security audits
Cloud security posture management (CSPM)
Cloud workload protection platform (CWPP)
Cloud sandboxing
Artificial intelligence
Machine learning
Malware Protection in Cloud Computing: The Way Forward
As cloud computing continues to shape the future of technology, the need for robust malware protection in cloud computing infrastructure becomes increasingly pressing. By embracing a multi-layered approach that combines traditional security controls with cloud-specific measures, organizations can effectively safeguard their cloud-based systems from cyber threats, ensuring the reliability and security of their infrastructure and operations.






![Free Cybersecurity Courses & Certificates [2026] | Coursera Free Cybersecurity Courses & Certificates [2026] | Coursera](https://blog.vcloudtech.com/wp-content/uploads/2023/02/What-is-Malware-Protection-1920x1080-782x440.jpg)