Email Protection Methods: Essential for a Secure Digital Age
As the world becomes increasingly dependent on email communication, the need for robust email protection methods has never been more critical. Email security threats, such as phishing, malware, and data breaches, can have devastating consequences for individuals and organizations alike. In this article, we will delve into the world of email protection methods, exploring the latest technologies, best practices, and expert advice to help you safeguard your email accounts and servers.
What are Email Protection Methods?
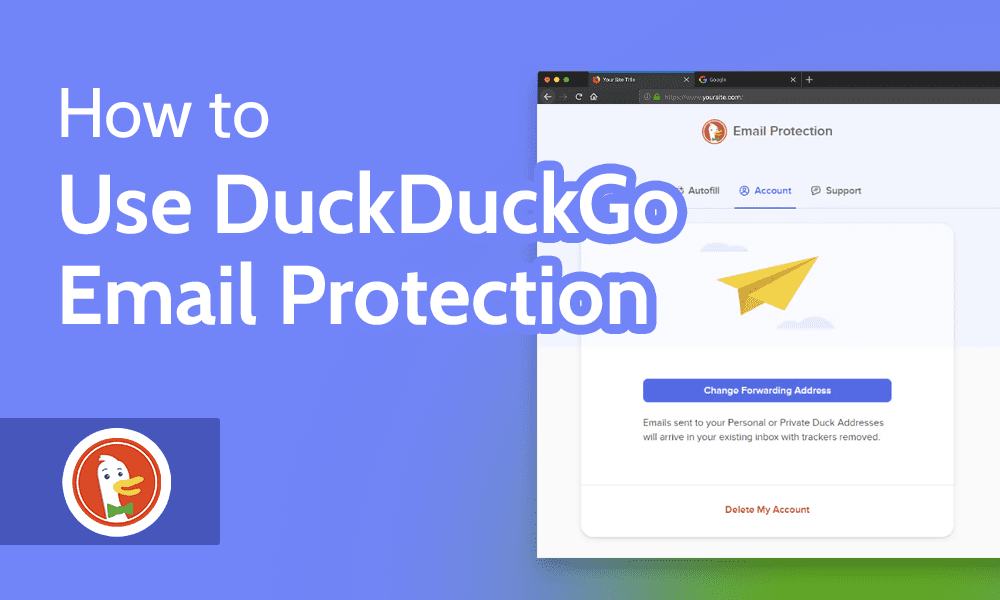
Email protection methods refer to a range of techniques, tools, and practices designed to secure email communications from various cyber threats. These methods can include email security software, encryption, two-factor authentication, and anti-spam techniques, among others. The primary goal of email protection methods is to prevent unauthorized access to email accounts, data, and systems, while ensuring the integrity and confidentiality of email communications.
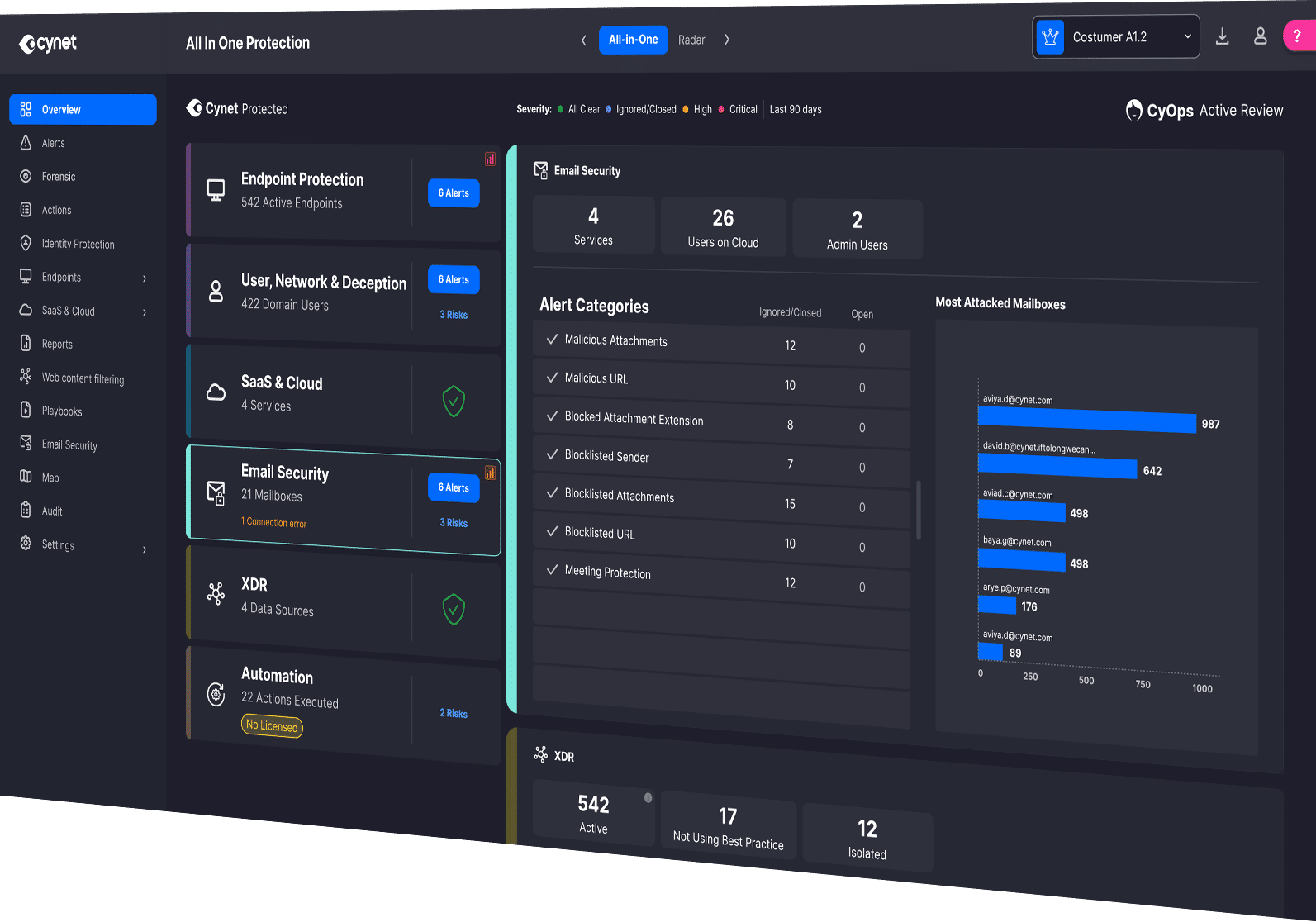
Integrated Cloud Email Security (ICES)
With the dominance of cloud email providers like Microsoft 365 and Google Workspace, ICES solutions that natively integrate with these platforms are gaining prominence. These solutions offer API-based protection that complements or enhances built-in security, providing a robust layer of email protection.
Types of Email Security Solutions
The four most common types of email security solutions include:
- Email security gateways
- Encrypted email services
- Email filtering services
- API protection
Email security gateways, for instance, are analytic programs that redirect emails, check them, and then forward them to the correct user or account. Security gateways help to identify threats in the email stream, preventing malicious emails from reaching your inbox.
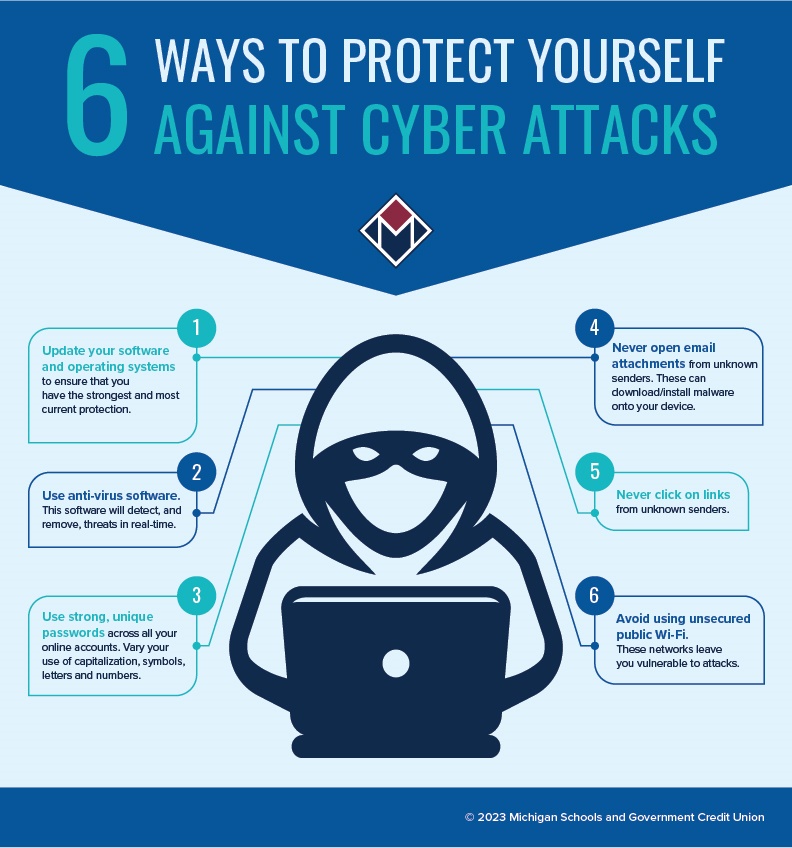
Authentication Methods

In addition to passwords, authentication methods like multi-factor authentication (MFA) provide an added layer of protection to secure email accounts. MFA requires users to provide two or more verification factors to access their email accounts, making it much more difficult for attackers to gain unauthorized access.
Authentication Policy
The authentication policy is the recommended way to manage authentication methods, including modern methods like passwordless authentication. Authentication Policy Administrators can edit this policy to enable authentication methods for all users or specific groups, ensuring that all users have a robust authentication process in place.
SPF, DKIM, and DMARC
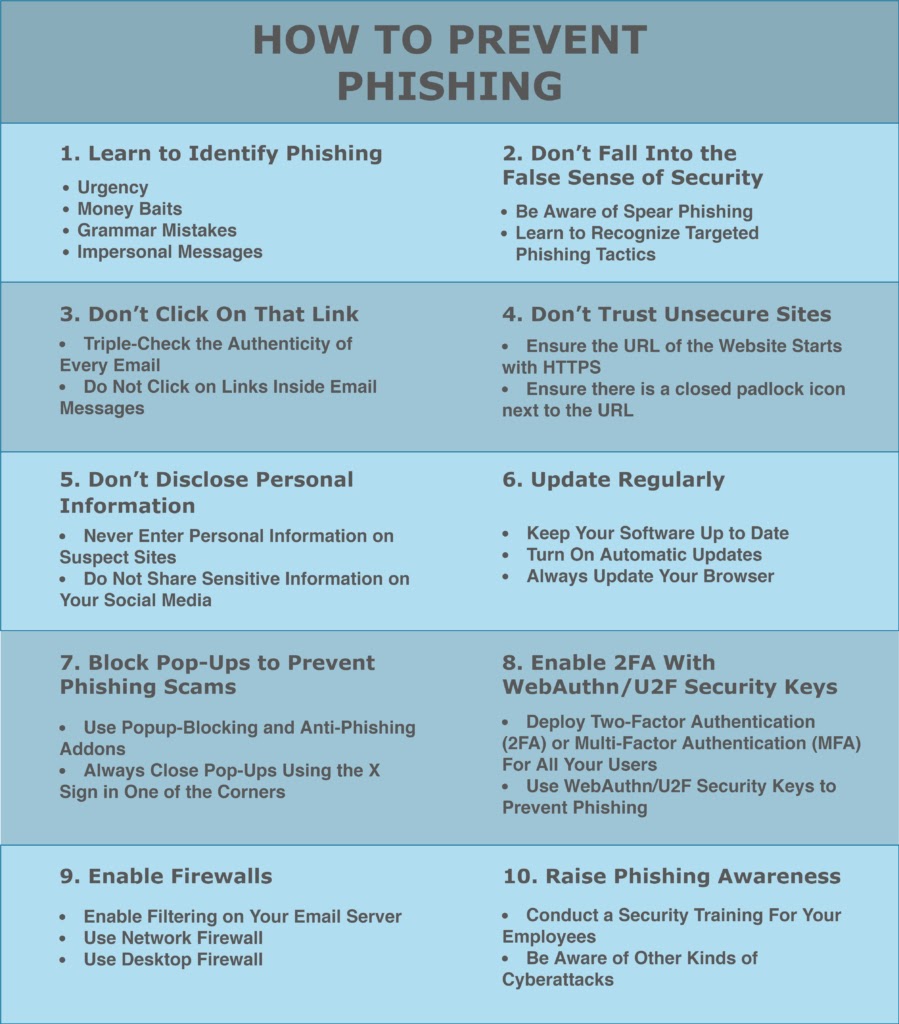
SPF, DKIM, and DMARC help authenticate email senders by verifying that the emails came from the domain that they claim to be from. These three authentication methods are essential for preventing spam, phishing attacks, and other email security risks.
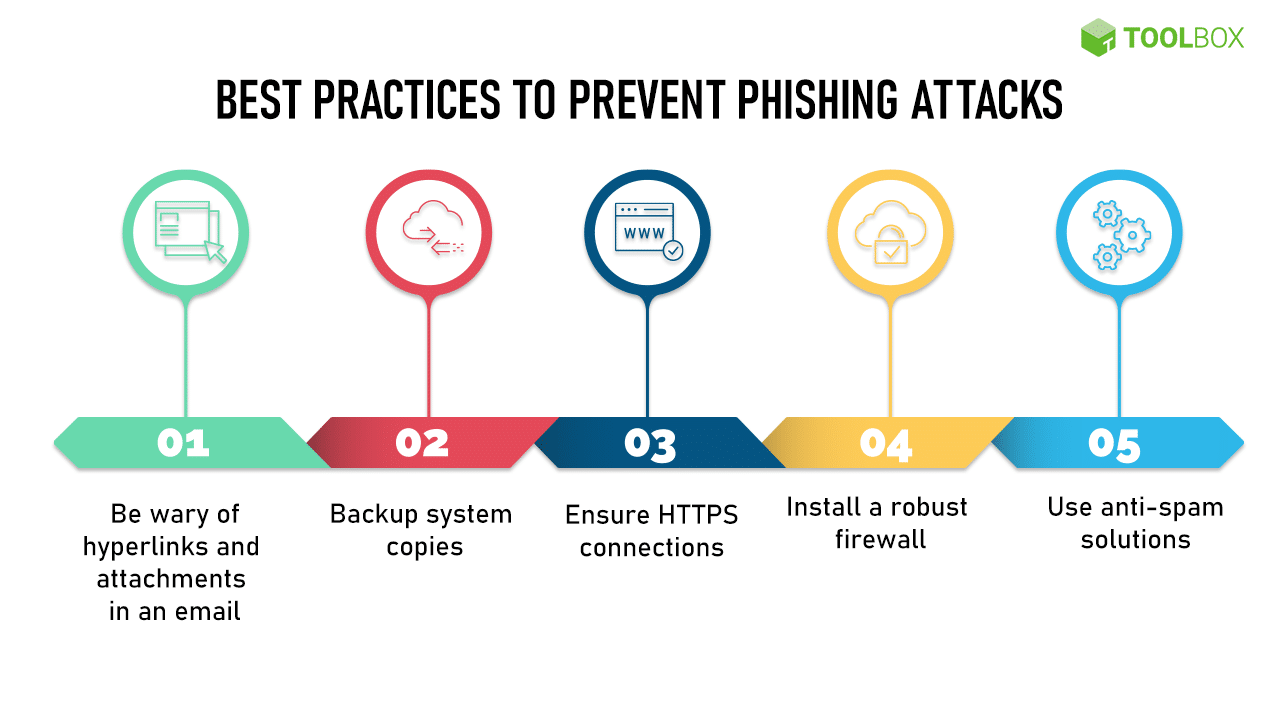
Best Email Security Practices
To ensure your email accounts and servers are secure, follow these best email security practices:
- Use strong passwords and MFA
- Implement email security software and encryption
- Use anti-spam techniques
- Regularly update your email client and software
- Monitor your email accounts for suspicious activity
Conclusion
Email protection methods are essential for securing email communications and preventing cyber threats. By understanding the various email protection methods, including ICES, email security gateways, authentication methods, and SPF, DKIM, and DMARC, you can safeguard your email accounts and servers. Remember to follow best email security practices to ensure your digital communications remain secure and confidential.





![Top 11 Email Security Best Practices for Businesses [2025] Top 11 Email Security Best Practices for Businesses [2025]](https://cdn.slidesharecdn.com/ss_thumbnails/howaiistransformingemailsecurityin2025-250814054535-39330718-thumbnail.jpg?width=640&height=640&fit=bounds)